Non-custodial wallet infrastructure is the software layer that lets applications create and manage wallets where users — not the provider — control the private keys. It matters because whoever controls the keys controls the funds. Picking a non-custodial stack means your users keep their own keys. Picking one that's also open-source means you can verify that claim instead of taking it on trust.
Custodial vs non-custodial: what's actually at stake
Most teams evaluate wallet infrastructure on features: gas sponsorship, account abstraction support, SDK quality. Those matter. But the decision that will haunt you three years from now is the custody model — specifically, how much you can verify about it.
There are three tiers:
| Custodial | Non-Custodial (Closed-Source) | Non-Custodial (Open-Source) | |
|---|---|---|---|
| Who holds keys | Provider | User (via provider's code) | User (via auditable code) |
| Audit trail | None | Limited — trust the vendor | Full — read the code |
| Vendor dependency | Total | High | Low |
| Migration path | Provider controls | Difficult | Fork and self-host |
| Regulatory stance | You're the custodian | User is custodian | User is custodian, and it's provable |
| Security model | Trust the provider entirely | Trust the provider's claims | Verify the implementation |
The distinction between the second and third columns is the one most teams miss.
"Non-custodial" means the provider doesn't hold your users' keys. That's the claim. But if the key management code is closed-source, you're trusting a black box to deliver on that claim. You can't audit it. You can't verify it. You can't prove it to a regulator or to your users.
Non-custodial plus open-source is the only combination that actually delivers on the promise of user-controlled keys. Everything else is a trust exercise with varying degrees of comfort.
The vendor lock-in problem in wallet infrastructure
Wallet infrastructure isn't a commodity you swap out like a payment processor. Your users' keys live in this system. Their accounts are derived from it. Their transaction history, session keys, and recovery mechanisms are all tied to your provider's architecture.
That means lock-in in wallet infrastructure is qualitatively different from lock-in in other parts of your stack. Here's what it looks like in practice.
When your wallet provider gets acquired
When a wallet provider is acquired, its roadmap serves the acquirer's priorities, not yours. Features you depend on get deprioritized. Pricing changes to align with the parent company's monetization strategy. The team that built the product you chose may leave.
This isn't hypothetical. It's the natural outcome of any acquisition. The acquiring company bought the provider for its own strategic reasons, and those reasons rarely align with your product roadmap.
If the code is closed-source, you have no fallback. You can't fork the last good version and maintain it yourself. You're along for the ride.
When pricing changes
Closed-source infrastructure gives the provider total pricing power. You can't self-host. You can't run a fork. You can't credibly threaten to leave because migration is painful and risky. The provider knows this.
With open-source infrastructure, pricing stays honest. If a provider raises prices beyond what's reasonable, you have the option to self-host. You may never exercise that option, but its existence keeps the relationship balanced.
When roadmaps diverge
You need support for a new chain. Your provider is focused on a different market. You need a specific key derivation scheme. Your provider thinks it's a niche request.
With closed-source infrastructure, you file a feature request and wait. With open-source infrastructure, you fork the module, make your change, and optionally contribute it back. Your product isn't blocked by someone else's prioritization decisions.
When your provider goes down — or goes away
Startups fail. Products get sunset. Entire companies disappear. If your wallet provider shuts down and the code is closed-source, your users' key management layer vanishes with it.
With open-source key management, the code survives the company. You or anyone in the community can continue running it. User wallets remain accessible because the derivation logic, the signing code, and the recovery mechanisms are all public.
This isn't a theoretical concern. It's basic infrastructure risk management. The code that controls access to your users' funds should not depend on a single company's continued existence.
What open-source wallet infrastructure looks like
Open-source wallet infrastructure means the key management code — the part that generates, stores, and signs with private keys — is publicly available, auditable, and forkable.
Here's what that looks like in practice:
The key management code is public. Not just the SDK. Not just the client library. The actual key management module — the code that touches private keys — is open-source. Anyone can read it, audit it, and verify what it does.
You can fork it and self-host it. If you need to run key management on your own infrastructure, you can. If you need to modify the signing logic, you can. The code is yours to use.
Security comes from transparency. Closed-source key management relies on the assumption that the vendor's internal team catches every vulnerability. Open-source key management benefits from every security researcher, auditor, and developer who reads the code. More eyes on critical code means more bugs caught.
Improvements are community-driven. When one team builds a better recovery mechanism, every team benefits. When a security researcher finds an issue, it gets patched publicly. The ecosystem improves faster than any single vendor can.
There's no lock-in by design. You can't be locked into code you can fork. This isn't a side effect — it's a structural property of open-source infrastructure.
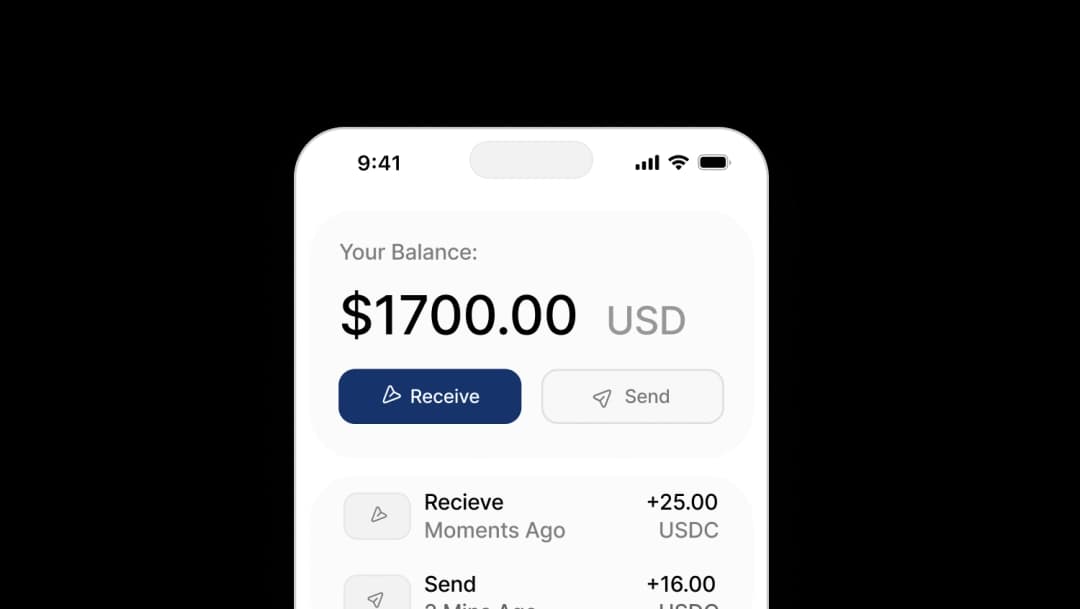
OpenSigner: what open-source key management looks like in production
OpenSigner is Openfort's open-source, non-custodial key management module. It handles key generation, storage, and signing — the critical path that touches private keys.
OpenSigner is the proof point that open-source key management works at production scale. It's not a demo or a reference implementation. It's the same key management layer that Openfort runs in production, published as open-source code.
What this means for you:
- Audit the code. Read exactly how keys are generated, stored, and used. No trust required.
- Fork it. If Openfort changes direction or disappears, you have the code. Your users' wallets remain accessible.
- Self-host it. Run key management on your own infrastructure if your compliance or security requirements demand it.
- Modify it. Need a custom signing flow? Need to integrate with your own HSM? The code is yours to extend.
OpenSigner uses standard protocols — ERC-4337 for account abstraction, widely adopted key derivation schemes — so it's interoperable with the broader ecosystem by default. No proprietary formats that tie you to a single provider.
This is what "own your stack" means in practice. Not just using non-custodial infrastructure, but being able to verify, fork, and run that infrastructure independently.
How to evaluate wallet infrastructure for lock-in risk
Before you commit to a wallet provider, run this checklist. It applies to any provider, including Openfort.
Lock-in risk scorecard
| Question | What you want | Why it matters |
|---|---|---|
| Is the key management code open-source? | Yes | If it's closed, you can't verify custody claims or fork it |
| Can you export user keys or key shares? | Yes, with documented process | If you can't export, migration requires users to re-onboard |
| Can you self-host the key management layer? | Yes | Self-hosting is your escape hatch from pricing and roadmap changes |
| Is there a documented migration path? | Yes, with tooling | "You can migrate" means nothing without documentation and tooling |
| What happens to user wallets if the provider shuts down? | Keys remain accessible | If wallets die with the provider, that's a single point of failure |
| Does the provider use standard protocols or proprietary ones? | ERC-4337, standard derivation schemes | Proprietary protocols create technical lock-in |
| Is pricing transparent and predictable? | Published pricing, no hidden fees | Opaque pricing plus high switching costs equals leverage against you |
How to use this scorecard
Score each question as green (fully met), yellow (partially met), or red (not met). Any red on the first three questions — open-source, exportable keys, self-hostable — is a structural lock-in risk that no amount of good customer support will fix.
The best providers will encourage you to run this evaluation. They have nothing to hide. If a provider pushes back on these questions or answers them vaguely, that tells you something.
Openfort scores green on every item. OpenSigner is open-source. Keys are exportable. Self-hosting is supported. ERC-4337 is the default. But don't take our word for it — run the checklist yourself. That's the point.
The regulatory angle
Regulators worldwide are drawing sharper lines between custodial and non-custodial infrastructure. MiCA in the EU, evolving frameworks in the US and Asia — all treat non-custodial services differently from custodial ones, typically with lighter regulatory requirements.
But "we're non-custodial" is becoming insufficient as a compliance position. Regulators want evidence. They want to understand how key management works, who has access to what, and what happens in failure scenarios.
Open-source key management gives you a stronger compliance position for three reasons:
- Auditability. Regulators or their auditors can read the code. They don't have to trust a vendor's claims about their architecture.
- Provability. You can demonstrate — with code — that your infrastructure is non-custodial. No black boxes, no "trust us" handwaves.
- Continuity. Regulators care about what happens to consumer funds if a provider fails. Open-source code that can be forked and self-hosted is a concrete answer to that question.
As regulatory frameworks mature, the gap between "non-custodial by claim" and "non-custodial by verifiable code" will matter more, not less. Building on open-source infrastructure now is a regulatory hedge that costs you nothing.
Openfort's key management module, OpenSigner, is open-source and non-custodial. Audit the code, fork it, or use it as-is. Your stack should be yours.